How to Stop Business Email Compromise (BEC) with Defend
Business email compromise is the most common phishing threat
37%
of cybercrime losses reported to FBI caused by BEC threats
98%
of cyberattacks involve social engineering
$43bn
has been lost due to BEC attacks
What is Business Email Compromise?
BEC threats are the hardest phishing attacks to detect. Threat actors impersonate or hijack a legitimate business email account that belongs to a trusted vendor, CEO, or another executive, using social engineering to trick their target into fraudulently transferring funds or divulging sensitive information.
The signature-based detection in Microsoft 365 native security and secure email gateways (SEGs) cannot detect BEC attacks at the rate modern enterprises need to prevent financial losses, data exfiltration, and reputational damage.
In 2021, the FBI reported nearly $2.4B in losses as a result of BEC and 66% of organizations suffered a successful attack.
- "Fighting Phishing: The IT Leader's View"
Defend uses intelligent technology to detect BEC attacks
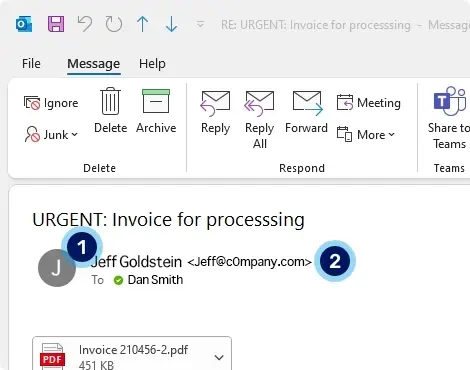
1. Display name impersonation detection. This is difficult for users to spot, especially on mobile devices, and as the domain is real, it passes SPF checks.2. Homograph attack. The domain c0mpany.com is used to fool the user into thinking this BEC threat is a genuine email. However, the display name matches that used by an internal user. An internal user with an external domain is treated with suspicion by Defend.
We’re really pleased with Defend. We’re now detecting a broader range of advanced phishing threats, including BEC and impersonation attacks.
Kevin Orritt, Cyber Security Manager, GMMH
Natural language processing (NLP) enhances BEC detection
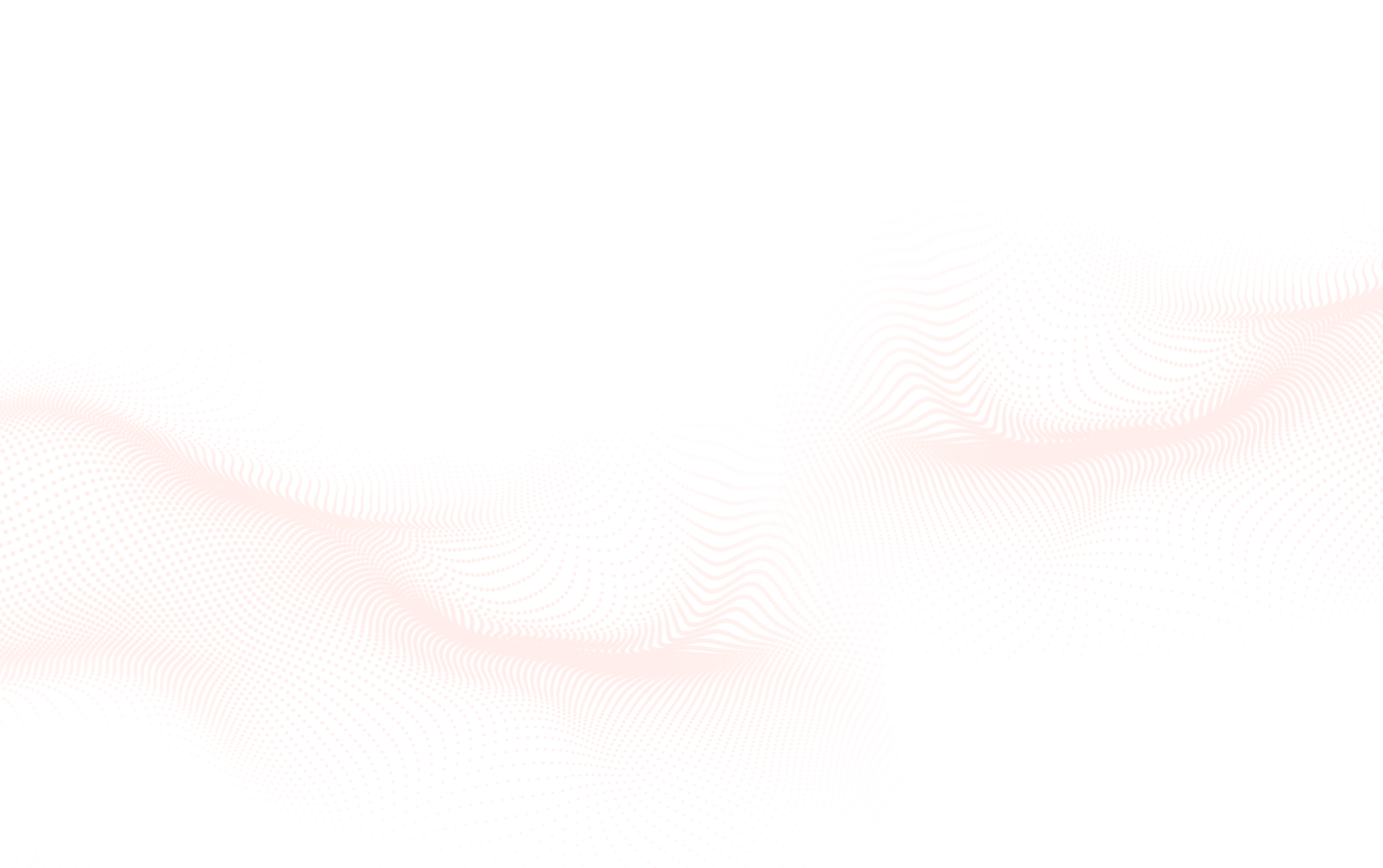
3. Linguistic analysis. Defend detects that the language used in this email includes credibility statements that incite a sense of urgency and try to deter the user from confirming legitimacy through other means.4. CEO impersonation. Using NLP, Defend detects that the attacker is posing as the CEO to appear as a trusted and important sender to try to increase the likelihood that the user will engage.
Cut through the noise to highlight the risks that matter
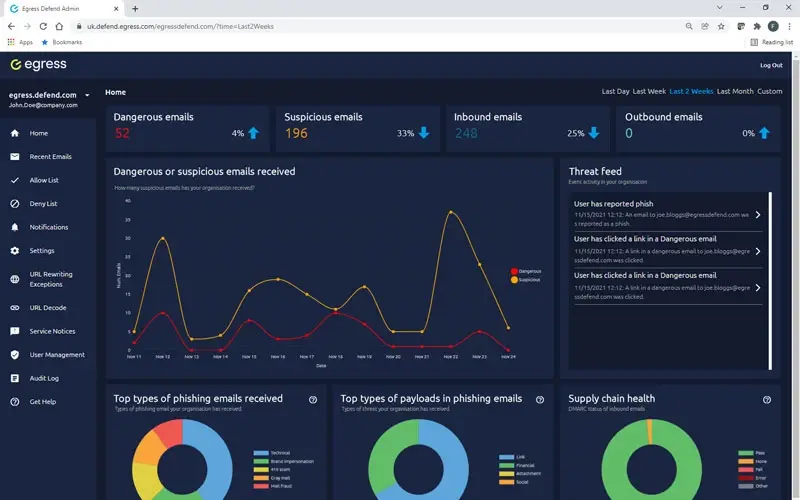
Reporting on BEC threats and other phishing attacks can be manual and slow. Even worse, systems can throw too much unnecessary information at you, making it harder to make timely and effective decisions.
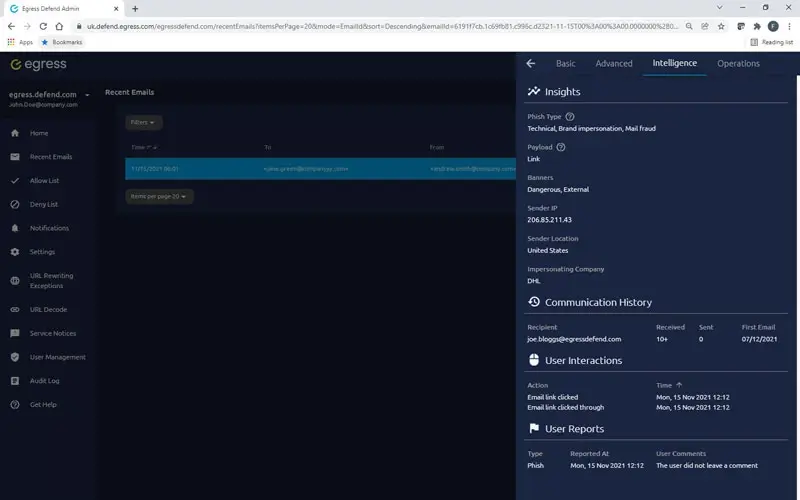
Defend’s intelligence platform provides simplified dashboards and critical insights so that administrators can quickly cut through the noise, identify email security risks, and, where necessary, remediate them.
Actionable intelligence into BEC threats
Data and analytics should not overwhelm you with information. Augmented threat intelligence into attack types, payload, and supply chain health gives Security teams what they need to take decisive action that mitigate BEC threats.
Our real-time threat feed offers insights and statistics into email details, type of attack, threat levels, authentication checks, communication history, and how your people interacted with the email.
Frequently Asked Questions about BEC
What is Business Email Compromise (BEC)?
Business Email Compromise (BEC) is an advanced type of phishing attack where threat actors impersonate or hijack legitimate business email accounts to trick targets into transferring funds or divulging sensitive information. Unlike standard spam, BEC is highly targeted and relies heavily on social engineering.
In practice, attackers will often pose as trusted vendors, CEOs, or executives. Because they mimic established relationships, these attacks circumvent traditional security protocols. According to the FBI, BEC is the most common phishing threat and resulted in nearly $2.4 billion in losses during a single year.
A strong defense requires specialized tools that understand context, rather than just simple malicious links.
What is the difference between business email compromise (BEC) and phishing?
Business Email Compromise is actually a specific, highly sophisticated subset of phishing, but it differs fundamentally in execution. While traditional phishing casts a wide net using malicious attachments or links, BEC relies almost entirely on text-based social engineering without a clear technical payload.
For example, instead of sending malware, a BEC attacker might email the finance department posing as the CEO, urgently requesting a wire transfer for a "confidential acquisition." The lack of traditional malware makes it nearly invisible to standard filters. In fact, 98% of cyberattacks involve this type of social engineering.
Defending against it requires moving beyond basic URL scanning and into behavioral and linguistic analysis.
Why are BEC attacks hard to detect?
BEC attacks are exceptionally difficult to detect because they lack the traditional indicators of compromise, such as malicious attachments or suspicious URLs. Since attackers often utilize text-only emails sent from seemingly legitimate sources, standard security measures are bypassed.
In practice, an attacker might use display name impersonation. They send an email using a legitimate domain—meaning it passes SPF authentication checks—but change the sender display name to match a company executive. On mobile devices where only the display name is visible, this is incredibly difficult for an employee to spot.
Signature-based detection in platforms like Microsoft 365 or traditional Secure Email Gateways (SEGs) frequently fail to catch these subtle variations.
How do BEC attacks bypass standard email security?
BEC attacks bypass standard email security like Secure Email Gateways (SEGs) and default Microsoft 365 protections because they don't trigger signature-based alarms. Standard security scans for known malware signatures or blacklisted URLs.
Attackers bypass this by utilizing legitimate infrastructure. For example, they may register a new, clean domain that closely resembles your vendor's domain, or they might successfully compromise a legitimate vendor account and email you directly from it. Since the sender's domain has a good reputation and no malicious payload is attached, the SEG waves it right through.
Stopping this requires technology that scrutinizes the *intent* of the message, not just the technical metadata.
What is an example of business email compromise?
One of the most frequent and damaging examples of business email compromise is CEO Impersonation. In this scenario, an attacker researches the company hierarchy and targets an employee with financial authority.
For instance, an attacker might send an email to the Accounts Payable manager with the display name of the CEO. The email uses urgent language to request immediate payment of a fake invoice to a newly established bank account, bypassing normal approval channels due to "extenuating circumstances."
Another common example involves look-alike domains—such as an attacker using c0mpany.com instead of company.com to deceive an employee into thinking an external email is actually internal.
How does natural language processing (NLP) stop BEC?
Natural Language Processing (NLP) stops BEC by analyzing the actual context and intent of the words used in an email, rather than just looking at technical headers or links. It allows security systems to "read" the email similarly to how a human would.
In practice, the KnowBe4 Defend platform utilizes NLP to identify "credibility statements." These are specific phrases used by attackers to incite urgency, demand secrecy, or discourage the recipient from verifying the request offline. Furthermore, NLP can detect when an external sender is assuming the persona of a high-value executive.
By understanding linguistic patterns, NLP catches the social engineering tactics that form the core of a BEC attack before the user ever sees the message.
How do look-alike domains factor into BEC attacks?
Look-alike domains, also known as Homograph attacks, are a primary tactic in BEC designed to deceive the human eye. Attackers register a domain name that looks almost identical to a trusted organization's domain, often by swapping similar characters.
For example, an attacker might substitute a lowercase 'L' for a number '1', or use a zero instead of the letter 'O'. If an employee receives an email from billing@microsoft.com versus the fake billing@micros0ft.com, they are highly likely to miss the discrepancy.
Advanced ICES platforms like Defend automatically flag these discrepancies, treating external emails that attempt to mimic internal usernames with extreme suspicion, cutting off the attack path.
What impact do BEC attacks have on businesses?
The impact of BEC attacks on businesses is severe, frequently resulting in massive financial losses, compromised supply chains, and significant reputational damage. It is currently one of the most lucrative forms of cybercrime.
The scale is staggering: globally, an estimated $43 billion has been lost to BEC attacks. Furthermore, data indicates that 37% of all cybercrime losses reported to the FBI are directly caused by these threats. In 2021 alone, 66% of organizations suffered a successful attack.
Deploying intelligent technology that leverages actionable intelligence is no longer optional for businesses aiming to protect their bottom line and their trusted relationships.